The Cloud service has been engineered to take full advantage of modern cloud computing concepts. Running on AWS, the service is distributed over multiple regions and availability zones. Under load the processing scales across multiple servers to provide a high-availability and reliable service.
The Cloud also provides a convenient web portal, useful for initial evaluation and ongoing template/account/billing/user management.
The service has been designed to efficiently perform transactional requests, generating single-page documents sub-second, or to meet large batch processing requirements and is capable of generating hundreds-of-thousands of documents-per-hour.
# Use the Docmosis Cloud service running in the US region
url = URI(“https://us1.dws4.docmosis.com/api/render”)
http = Net::HTTP.new(url.host, url.port)
http.use_ssl = true
http.verify_mode = OpenSSL::SSL::VERIFY_NONE# Specify data to be merged with the template
JSON_DATA='{“message”:”This Cloud API is working great!”}’;# Create the POST request
request = Net::HTTP::Post.new(url)
request[“Content-Type”] = ‘application/json’# Add accessKey, data, template and output file / format to the request
request.body = “{” +
“\”accessKey\”: Y2QxNj1hMzYtOaM2YxtMjJlxGyMjI0NjVOrMTAzjU\”, ” +
“\”templateName\”: \”myTemplate.docx\”,” +
“\”outputName\”: \”result\”,” + “\”outputFormat\”: \”PDF\”,” +
“\”data\”:#{JSON_DATA}}”# Call Cloud with the request and save the response as a file
response = http.request(request)
An API-First Approach
The service was designed knowing that it would primarily be used via the API.
The API has been structured to make it easy to use, whether:
- Configuring a webhook in a third-party app.
- Calling the API by writing code.
This makes it possible to use the service from most modern platforms:
- Custom Software Applications (Java, .Net, PHP, Ruby, Python, etc)
- Third-Party Apps (CRMs, Webforms, Workflow Automation, etc)
- Low-Code/No-Code Apps (Appian, Mendix, Bubble, Out Systems, etc)
By default, generated documents are returned to the calling application, allowing the application to perform further actions with the file(s). Other delivery options include:
- Delivery via email.
- Stored to an AWS S3 Bucket.
- Sent using a webhook to third-party services.
The API provides endpoints to perform other tasks, such as: upload, download, list and delete templates; query the structure of a template and return the field names; and check the status of the service and account.
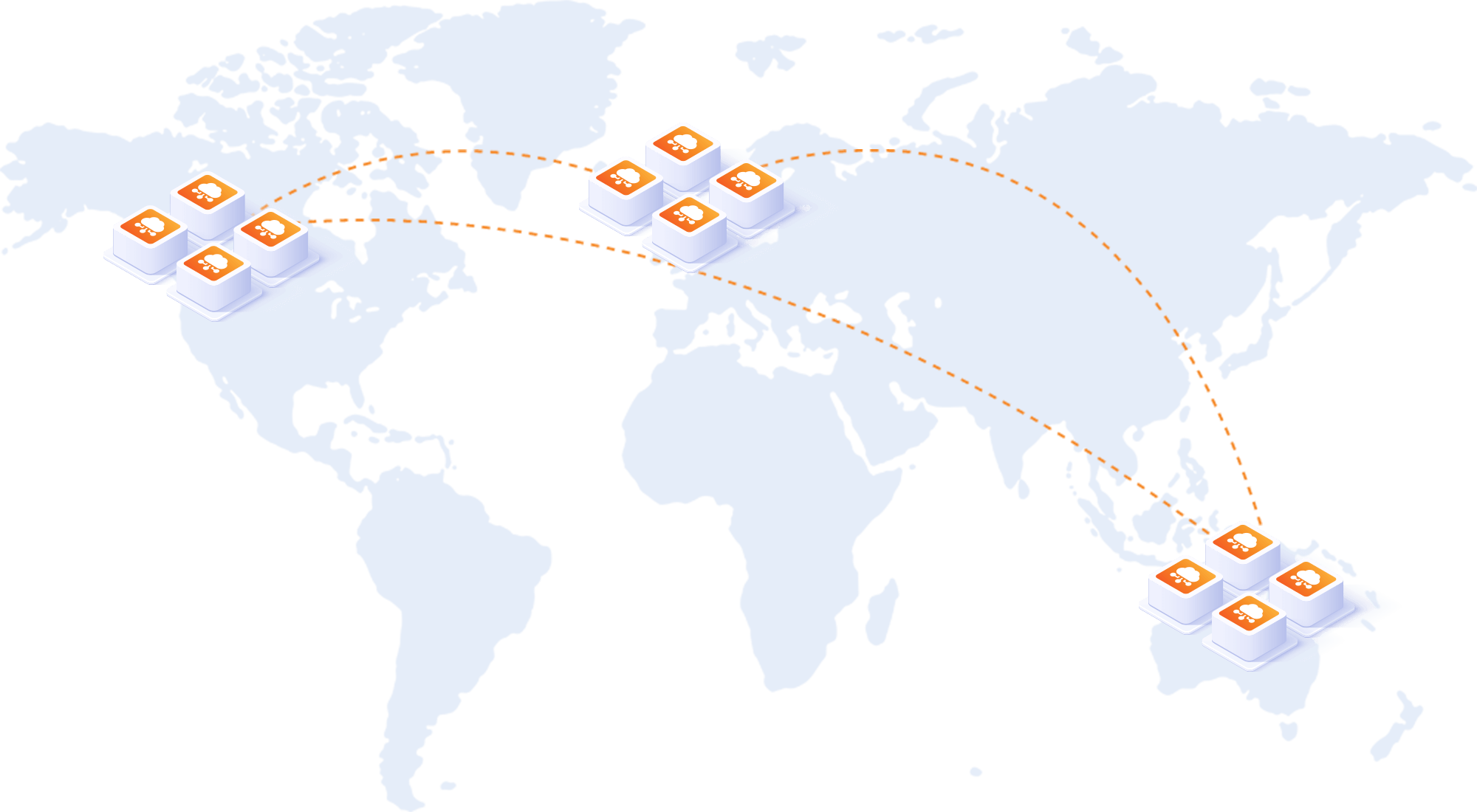
Processing Locations
The cloud advantages of high-availability, increased reliability and scalability, naturally lead to questions about data residency.
US Region = https://us.dwsX.docmosis.com/api/xxx
Cloud users can select the physical location used for storing templates/images and control where processing occurs, via the:
- Cloud Console – a convenient web portal for uploading templates and testing documents.
- Document Generation API – the base URL determines the region.
A single Cloud account enables the service to be used in all available regions (United States, Europe and APAC). Users may choose a region for low-latency/high performance or to satisfy data residency requirements.
US Region = https://us.dwsX.docmosis.com/api/xxx
Cloud is the easiest way to try Docmosis making it perfect for initial evaluation and rapid proof-of-concept work. Teams that prefer a self-hosted solution can also consider Tornado, which provides similar API endpoints, making it easy to move from Cloud to Tornado when ready.
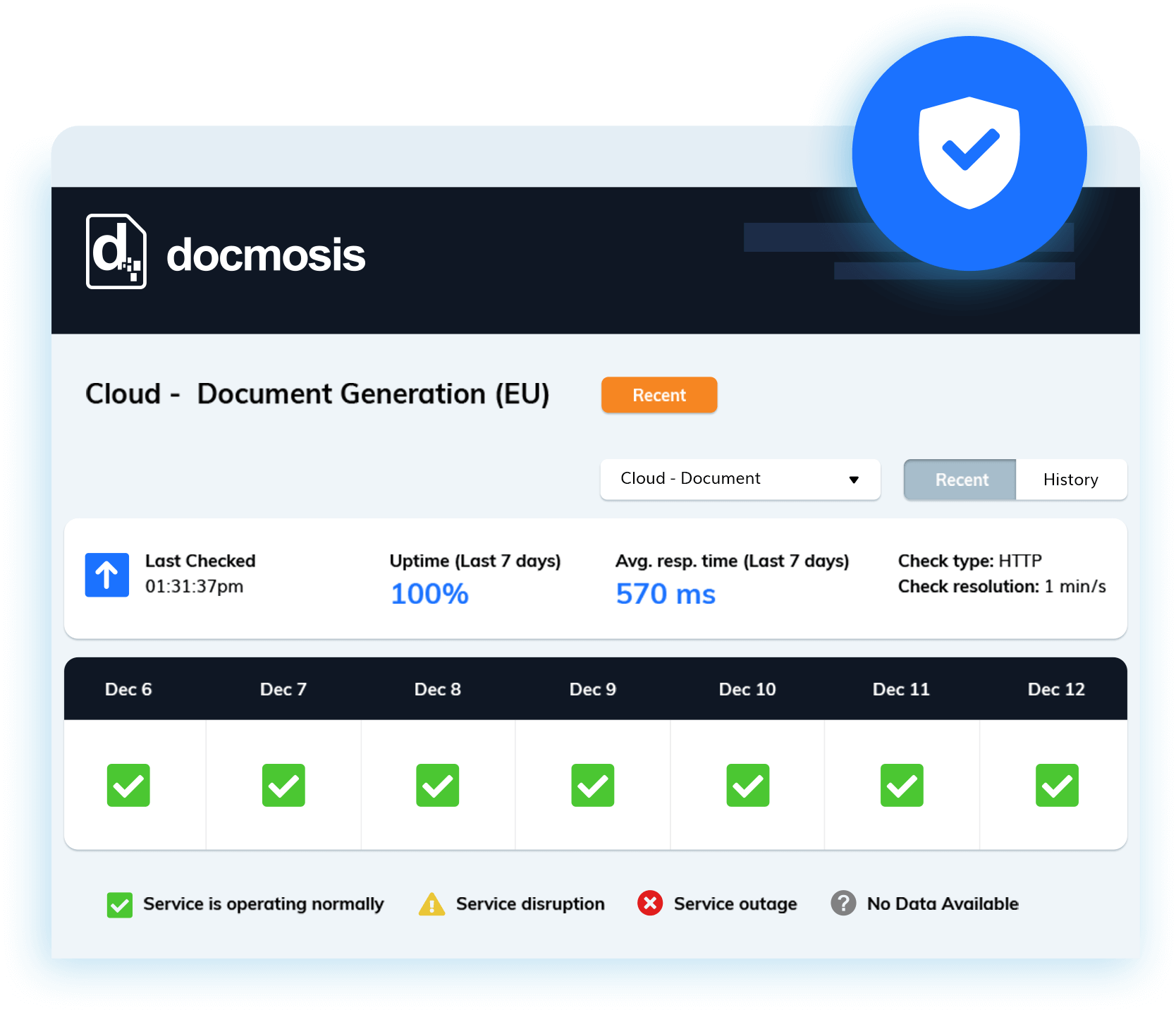
Uptime Monitoring
Document production is often mission-critical.
Any service must be stable, consistent and always available.
Since 2016 the Cloud service has been monitored 24/7, using the third-party platform Pingdom, by generating a test document every 60 seconds.
View years of publically available historical uptime records. The results show the time taken to complete a deep-test, that activates the rendering engine, and return a single-page document.
Cloud Versions
The first version of the service was launched in 2011 as Docmosis Web Services (DWS).
During the life of any given version all feature additions, environment changes and bug fixes are thoroughly tested to ensure there is 100% consistency in output for all existing users of the service.
Improvements, that can’t be safely applied to the current version, accrue over time and are released as a new version of the service (DWS2, DWS3, DWS4, etc.) that runs in parallel to the previous services.
Getting Started
No credit card, no watermarks, no limitations.
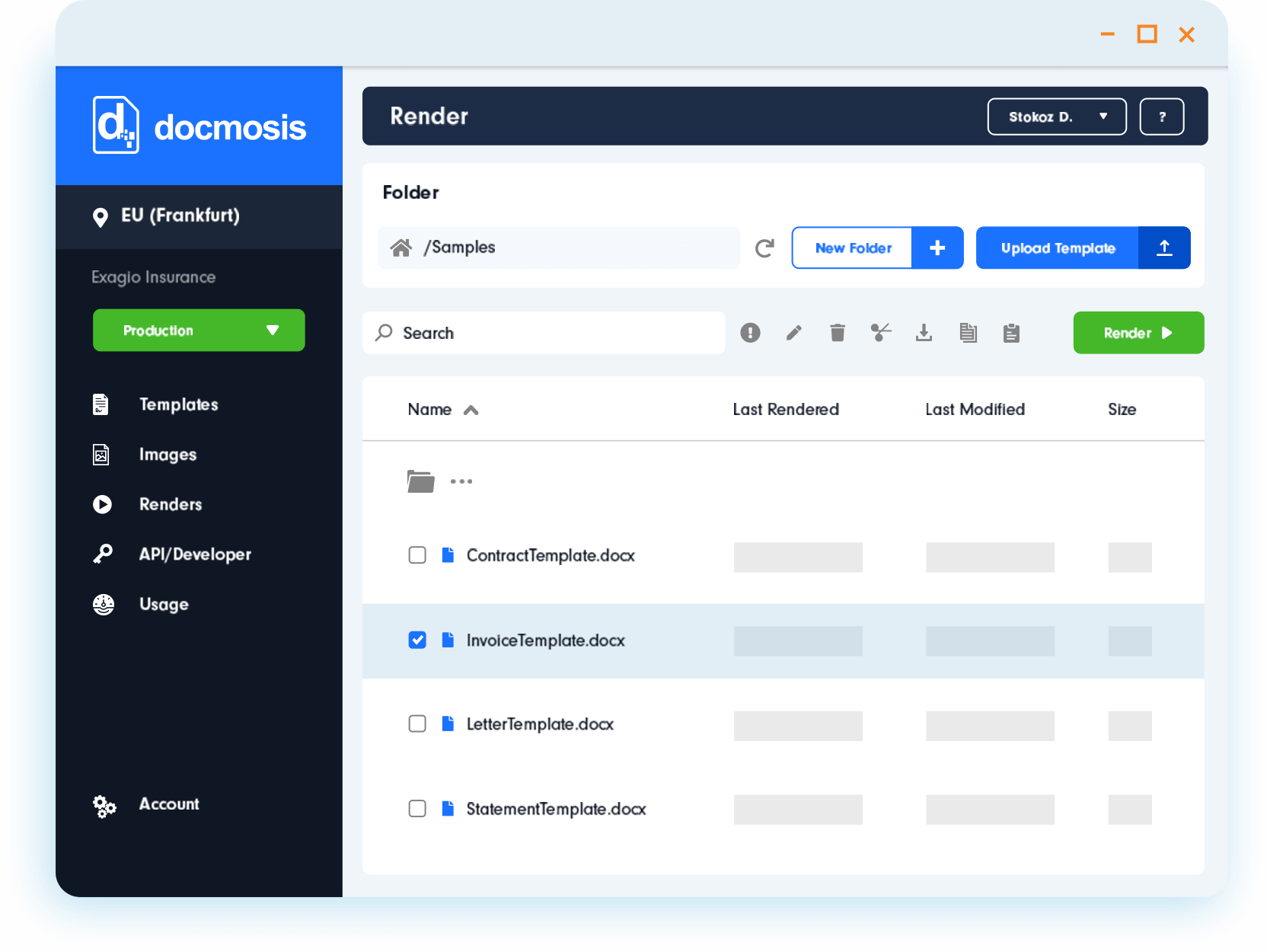
Start a free trial and use the service for 30 days, with the option to extend your evaluation if needed. With a trial account you can:
- Download, upload and manage templates and images
- Test the generation of documents from within the Cloud Console
- Create and manage API keys
- Call the API to generate documents
Follow the instructions on our Resources Website to help you get started.
Minimise Data Exposure
Generate business-critical documents with an approach to security your team can rely on.

- Automatic data deletion. Input data and generated documents are deleted immediately after processing.
- Secure by design. Templates are encrypted at rest, with HTTPS enforced for all communication.
- Independent assurance. Our SOC 2 Type II report is available through the Trust Portal.


![Docmosis_Graph [final] (1) processing locations](https://www.docmosis.com/wp-content/uploads/2022/08/Docmosis_Graph-final-1.jpg)